Fireblocks Becomes First to Achieve CCSS v9.0 Certification at Level 3
We’re pleased to announce that Fireblocks is the first organization ever to have a system certified under Version 9.0 of the CryptoCurrency Security Standard (CCSS), the most current version of the standard, released in December 2024.
The certified system includes:
- Fireblocks Hot and Cold Vaults
- Fireblocks Secure Transfer
- Fireblocks Authorization Workflow
- Fireblocks Tokenization Engine
Fireblocks' system attained Level 3 certification as a Qualified Service Provider (QSP) - the highest attainable level - after undergoing a rigorous audit.
Why this matters: This certification shows that Fireblocks has implemented strong controls for managing and securing key material across its system, in line with the latest CCSS requirements.
Version 9.0 includes several important updates to the standard, and it builds on the strong foundation of earlier versions. Systems certified under v8.1 remain valid and have also demonstrated a high level of security through independent audit.
Shoutout to CCSSA Marc Krisjanous for another successful audit, CCSSA Phillip Moran, CFA for a successful peer review, and the Fireblocks team for setting the bar for what secure, independently-audited key management should look like under the version 9.0 of the CCSS.
As a reminder, this does not verify that another system which uses Fireblocks is CCSS certified at any level. Any third party who uses Fireblocks’ system must be audited for compliance in the areas where Fireblocks does not have control and certified (or not) in an audit for their cryptocurrency system.
Congratulations to the Fireblocks team on this industry-leading achievement!
👉 You can verify Fireblocks’ certification at: https://cryptoconsortium.org/completed-ccss-audits/
CCSS v8.1 Certification Eligibility Extended Through December 17, 2025
When CCSS v9.0 was released on December 17, 2024, it introduced major updates to requirements and audit expectations. While this version marks a strong step forward, the transition has impacted timelines for some teams already preparing for certification under v8.1.
To support those efforts, new system certifications may still be conducted under CCSS v8.1 if the Intent to Audit form is submitted by December 17, 2025.
What’s Changing
- New audits may use v8.1 or v9.0 until December 17, 2025.
- After that, all new audits must follow v9.0.
- The CCSS version number will continue to be listed publicly for each certified system.
Why This Matters
This extension, based on auditor and community feedback, gives organizations:
- Time to align with v9.0
- A clear path for in-progress v8.1 efforts
- Stability during the version transition
With the draft of v9.0 available three months before publication, this updated timeline provides a full year of visibility into the changes.
We appreciate the community’s input in shaping this decision and look forward to continued collaboration as we raise the bar for crypto security.
To learn more or begin a CCSS audit, visit https://cryptoconsortium.org/ccss
Decision Not to Include Proposed FIPs 140 Requirement in CCSS v9.0
During the CCSS v9.0 review process, a proposed new requirement, 1.05.2.3, was introduced:
“The key material is isolated from other operating systems and application processes to avoid unauthorized access or leakage of key material. CCSS Level 3 requires FIPS 140 or equivalent.”
After careful consideration, the CCSS Steering Committee has decided not to include this control in the final version.
Why?
This decision was guided by extensive community feedback, research from both our Advocacy Group and our Steering Committee, and technical analysis shared during the review period. The key issue was the requirement for FIPS 140 certification, which presented several technical limitations:
- FIPS does not support widely used cryptographic curves in the blockchain space, such as secp256k1.
- Many secure, well-designed implementations in the crypto space can’t align with FIPS requirements, even if they follow strong security practices.
- It lacked flexibility to support emerging cryptographic tools and protocols being adopted across the ecosystem.
FIPS certified hardware and devices may (and often should) still be used as an encrypted storage method for key material, but given the lack of support for commonly used blockchain and cryptocurrency algorithms, it doesn’t make sense to require them for isolation in an operational environment.
The Outcome
The principle of isolating key material remains important, and the Standard reflects an adaptable approach. With the removal of the FIPS-specific requirement, CCSS v9.0 supports a wide range of secure implementations.
This decision underscores what CCSS is all about: a community-developed, technically sound standard that evolves alongside the industry it serves.

C4 is enhancing the CryptoCurrency Security Standard (CCSS) with the introduction of the CCSS Implementer (CCSSI) certification. CCSSIs will help organizations prepare for audits by identifying security gaps and assisting with CCSS implementation prior to an audit taking place.
CCSSI vs. CCSSA: Defining Roles
- CCSSI (Implementer): Focuses on pre-audit readiness, security implementation, and remediation support.
- CCSSA (Auditor): Conducts formal audits, determines system designation, level, and CCSS certification.
This clear distinction ensures smoother, more effective audits.
New Training & Certification Updates
- CCSSI certification comes with its own exam and structured training.
- All new CCSSA candidates must complete an attestation of knowledge and CCSSA training before taking the exam.
- Training content will be continuously updated to align with CCSS revisions.
CCSS Roadmap: What’s Ahead
In Q1 2025, C4 is developing CCSSI certification & training, finalizing CCSS v.9.x, and updating training materials. CCSSI Certification and Training will launch in Q2 2025. Throughout the year, improvements to CCSSA and CCSSI training programs will ensure professionals stay up to date with the CCSS.
For more details, check out the full CCSS Roadmap for more information.
Expanding Excellence: CEP and CCSSA Exams Transition to New and Improved Testing Platform
Introduction
Following the successful launch of the Certified Bitcoin Professional (CBP) exam on our new and improved testing platform, CryptoCurrency Certification Consortium (C4) is thrilled to announce that the Certified Ethereum Professional (CEP) and the Certified Cryptocurrency Security Standard Auditor (CCSSA) exams have now been migrated as well! This transition not only enhances the user experience but also aligns with our commitment to maintaining the highest standards in cryptocurrency education and certification.
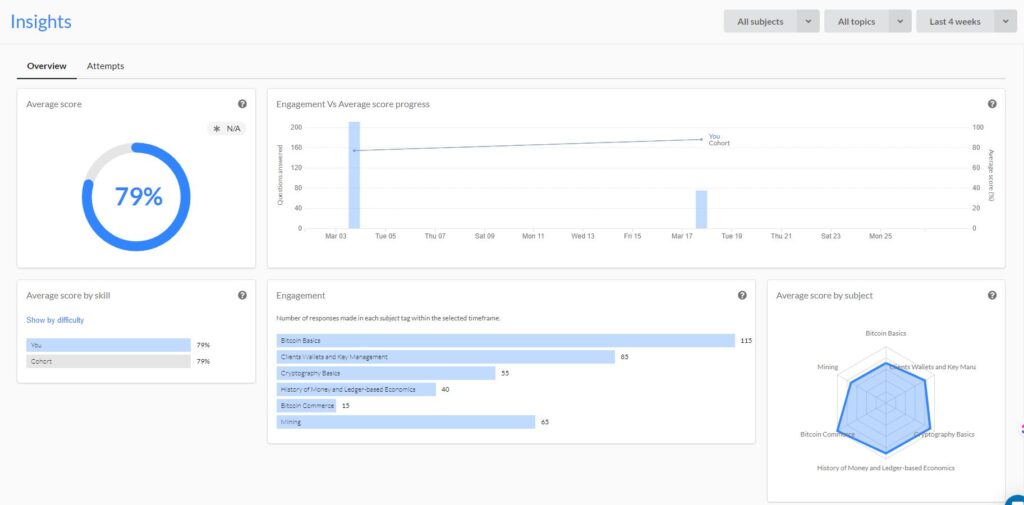
A Unified, Enhanced Testing Experience
The new platform delivers a seamless, intuitive user interface and valuable insights into test results, ensuring that every candidate experiences the most efficient and comprehensive testing process. With these upgrades, candidates for the CEP and CCSSA certifications will join the CBP candidates in enjoying the benefits of real-time scoring, instant feedback, and a flexible schedule for taking the exams online.
Updated Pricing Structure
In our ongoing effort to deliver exceptional value and quality, we are updating our exam and certification pricing. The revised fees will include the initial exam cost, one retake (if needed), as well as a digital certificate. Printed certificates will continue to be available for a nominal shipping fee.

Users who have already paid the exam fee with C4 will receive detailed information on next steps via email.
Special Offer for Renewing Candidates
Current CEPs and CCSSAs who are transitioning to the new platform may request a 50% off coupon. Subsequent renewals will be offered at 25% off. Additionally, during this transition, any prior CEPs and CCSSAs may request a 50% discount; the coupon will expire on August 1st, 2024.
To receive your coupon, please complete the renewal form using the email address previously registered with C4. Note that coupon codes will only be issued to the registered email addresses to maintain security and verification standards.
How to Proceed
To register for the CEP, CCSSA, or any other C4 exam, or to renew your certification, please visit our website. https://cryptoconsortium.org/get-certified/
Conclusion
C4's commitment to fostering professional growth and enhancing security practices within the cryptocurrency space continues with these exciting updates. Whether you are a new candidate aiming to certify your expertise or a returning professional seeking to renew and refresh your knowledge, our new platform and its features are here to support your journey in the cryptocurrency world.
If you have any questions or concerns, please contact us at certifications@cryptoconsortium.org.

Understanding the Bitcoin Halving
Bitcoin's protocol includes a ‘mining’ process where specialized computer hardware tackles complex mathematical problems to validate transactions and secure the network. Read on to understand nuances of this process, notably the Bitcoin halving, which is a programmed reduction in the block rewards miners receive, aimed at controlling the supply of new bitcoins and influencing economic factors like inflation and scarcity. As we approach another such halving, the interplay between technology and monetary policy within Bitcoin's architecture offers a compelling study of digital scarcity.
At the heart of Bitcoin's design is the mining process. Miners use specialized computer hardware to solve complex mathematical problems, validating transactions, and securing the network. Each block is added to the blockchain through this mining process and the first miner to correctly solve the problem for each block earns the block reward. Originally, miners were rewarded with 50 BTC for each block they successfully added to the blockchain, but the Bitcoin halving, a recurring event programmed into the Bitcoin protocol, reduces the block rewards that miners receive by half.
Bitcoin halvings occur approximately every four years, or after every 210,000 blocks have been mined. The most recent halving was in May 2020 and reduced the block reward from 12.5 to 6.25 BTC. The upcoming halving, anticipated in April 2024, will reduce the block reward from 6.25 to 3.125 BTC. This deliberate approach controls the supply of new bitcoin entering the system, thus influencing the inflation rate and the scarcity of bitcoin.
The halving plays a crucial role in the Bitcoin network's economic model. Satoshi Nakamoto, the pseudonymous creator of Bitcoin, designed the currency with a fixed supply of 21 million coins to prevent inflation and promote scarcity. The primary rationale behind Bitcoin halvings is to control the rate at which new bitcoin are generated, simulating a form of digital scarcity akin to precious metals like gold. The halving mechanism ensures that the creation of new bitcoin slows down over time, making Bitcoin deflationary by nature. This design contrasts sharply with fiat currencies, which central banks can inflate at will.
Ultimately the Bitcoin halving is much more than just a technical event within the cryptocurrency's network; it's a fundamental aspect of its economic model and a testament to its innovative approach to digital scarcity and monetary policy.
Disclaimer
The information presented in this article is for educational and informational purposes only. It does not constitute financial advice, investment recommendations, or any form of endorsement.
The views and opinions expressed by individuals in this article are solely those of the speakers and do not necessarily represent those of C4 or any other organizations with which they are affiliated.
The mention or inclusion of any individuals, companies, or specific cryptocurrency projects in this video should not be considered as an endorsement or promotion.
Regulations and legal frameworks around cryptocurrencies may vary in different jurisdictions. It is your responsibility to comply with the applicable laws and regulations of your country or region.
The CBP Exam is Upgrading to a Superior Testing Platform!
The CryptoCurrency Certification Consortium (C4) is committed to providing the best resources and tools for professionals proving their knowledge about Bitcoin technology. As part of our ongoing efforts to enhance your certification experience, we are pleased to announce that the Certified Bitcoin Professional (CBP) exam will now be available through an advanced testing platform.
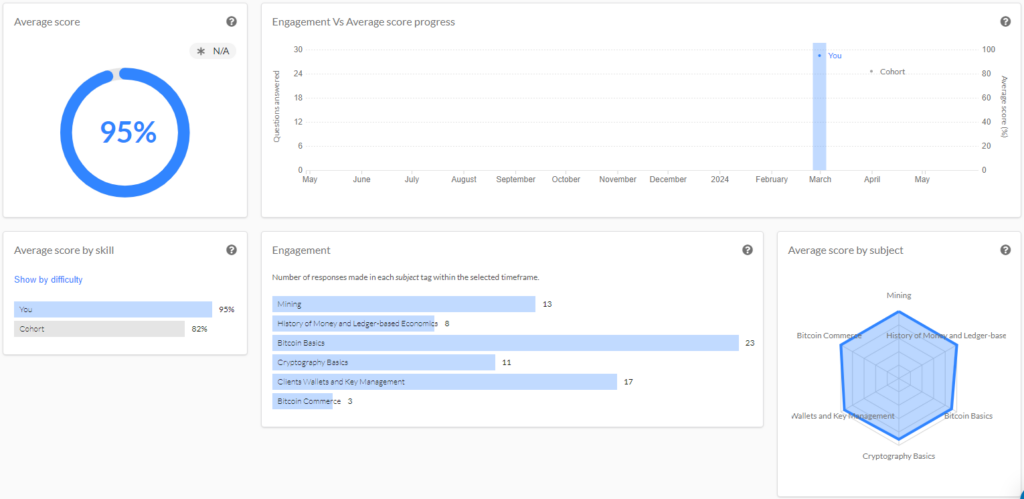
Enhancements to the CBP Exam Experience
The decision to transition testing platforms was to offer an improved testing process. Here are the key benefits of the new platform:
- Detailed Performance Insights: C4 now provides test-takers with comprehensive feedback on their performance across the six topics covered in the CBP study guide! This feature allows candidates to identify areas of strength and opportunities for further study, facilitating a more targeted preparation strategy.
- Digital Certificates: Reflecting the digital nature of the blockchain technology industry, CBP certifications will now be issued in digital format! This allows for easier sharing and verification of credentials. Paper certificates will remain available for those who prefer a physical copy.

- User-Friendly Interface: Our new platform offers a streamlined, intuitive testing experience. This ensures that candidates can easily navigate the platform, from registration to receiving results.
Update on CEP and CCSS Exams
Our Certified Ethereum Professional (CEP) and CryptoCurrency Security Standard Auditor (CCSSA) exams will remain on our existing testing platform for the time being. We are dedicated to ensuring a smooth and efficient transition for all our certifications and will be moving the CEP and CCSS exams in the coming months. This phased approach allows us to maintain the integrity and quality of the certification process, ensuring that every detail is addressed.
Getting Certified
We are excited about the enhancements to the CBP certification process! Detailed information on how to prepare for the CBP exam is available on our website at cryptoconsortium.org/CBP
For any questions or additional information, please do not hesitate to contact us. We are here to support your journey towards becoming a Certified Bitcoin Professional.
