Overview
Love crypto, but worry about its security? Cryptocurrency technologies are powerful because they allow you to hold your own keys for your money, rather than trusting a third party such as a bank. However, this opens up individual users to losses via scams and hacks that steal their crypto keys.
One very secure solution for individual key storage is a special device called a hardware wallet.
What makes these wallets so secure is that they generate these cryptocurrency keys entirely offline, and just for you. Rather than on a PC or mobile phone, that are more vulnerable to hackers, or with a 3rd party, such as an exchange. If you do not own your key, you do not own your money.
Hardware wallets, although great for security — are less ideal for day-to-day purchases. Which is why they are often used as savings accounts, versus ‘cash in your pocket’ functionality. These wallets are generally considered the most secure wallet for consumers, but care is required for proper use and storage of the keys. Here are some security pitfalls to be aware of.
Seed Phrase Management
The most important component of hardware wallet security is the management of the device’s seed phrase. A seed phrase is a collection of 12–24 words that serve as a critical backup of your wallet. This data grants access to all of the cryptocurrency balance stored in its wallet. So if you send 2 Ethereum and 1 Bitcoin to this wallet, the only way to restore access to the coins in the event your hardware wallet is lost or broken is to have a copy of the seed phrase.
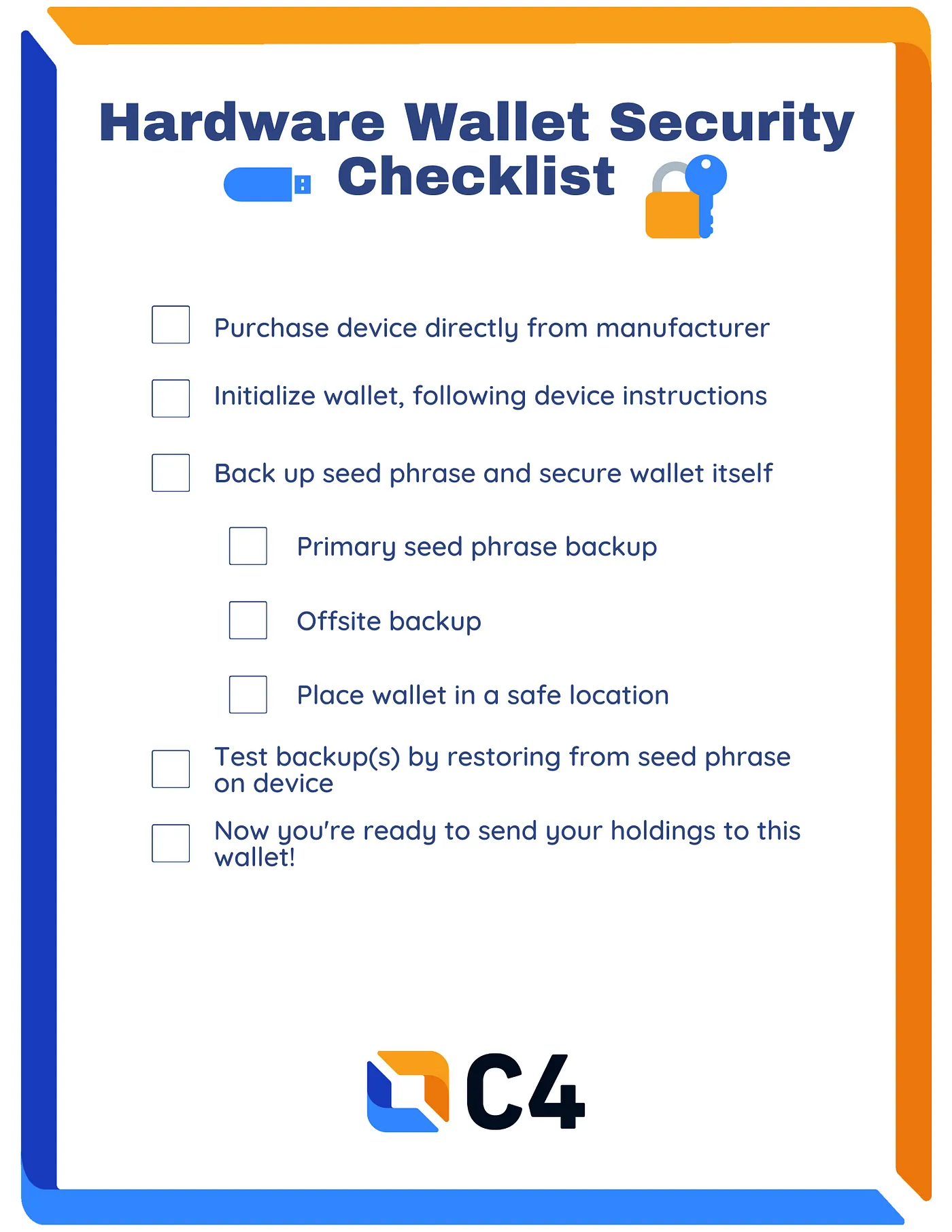
The first important item in our hardware wallet security checklist is to retain multiple copies of the seed phrase, not just the wallet itself. Seed phrases should be written on paper or engraved in metal, and stored in safe locations. One example might be a home safe, a hidden location in the home, or another location protected from fire/flood/theft. Another offsite location should be chosen, such as a bank safety deposit box, or the home of a trusted family member or friend. Both of these offsite locations require some level of trust — but offsite backups are critical in the event the original is destroyed. A bank safety deposit box may be seized, so a user may consider additional protection like a friend’s home or the addition of a BIP39 passphrase. The use of a BIP39 passphrase, stored in a separate location from the seed, can provide an additional layer of protection if the seed is compromised.
The second item in our checklist is the form of the seed phrase backup. Yes, how you backup your seed phrase is very important to your security. A hardware wallet seed should only be copied into a physical form such as paper or metal, never stored in a PC or mobile phone. If you use a hardware wallet, you should never store a copy of the seed in a picture, document, or even encrypted form such as a password manager. Why?
The entire purpose of a hardware wallet is to generate and store keys offline, on a device that doesn’t have access to the internet. A mobile phone or PC is connected to the internet, and offers general-purpose computing functionality. This offers a higher attack surface — more opportunities for hackers and thieves to gain access to your seed data and steal your cryptocurrency. By storing an offline wallet seed phrase on a general-purpose device like a PC, you break the security model of this offline wallet. So only backup your hardware wallet phrase in physical form!
Device Purchases and Management
Another noteworthy security practice for hardware wallets is how you purchase the wallet. These wallets run open-source software scrutinized by the cryptography and security community. But how can you know that the wallet is loaded with the same open-source software and not a malicious version?
The simplest way to protect against supply-chain attacks is to purchase these devices directly from the manufacturer (for example, Trezor). Do not purchase hardware wallets from third-party sellers such as Amazon or other online stores.
Phishing Awareness
Even though hardware wallets (with offline backups) are very secure, users are often tricked into giving up access to their coins via social engineering. For example, after the Ledger purchase database was compromised, users were targeted with various phishing scams. In one case, users were sent a fraudulent but legitimate-looking email asking them to “update their Ledger”. This led to a website that installs malicious software on their PC. Other similar campaigns prompt users to enter their 12–24 word seed phrases, giving the scammers full access to their wallets.
Never enter your seed phrase into any online form, even one that looks like it came from the manufacturer. Never install software on your device if requested by email, Twitter, etc. Never believe anyone claiming to be a support agent for a wallet. The only place you should read for software updates and support should be the manufacturer’s official website and support channels. Take your time when you need help — scammers want you to act quickly so they can trick you into giving up your coins.
Hardware Wallet Stories
Let’s suppose Alice has purchased 1 Ethereum and 0.5 Bitcoin she wishes to self-custody. Alice is primarily concerned with malware threats as she uses her PC for web browsing, and wants to keep her cryptocurrency wallets separate from her day-to-day devices. Alice purchases a Ledger device directly from the manufacturer, generates her seed, and writes it down on laminated paper. She stores one copy in a quality home safe, and another at her parent’s house. When she decides to sell half of her Ethereum, she connects her Ledger device to her PC to sign the transaction.
Bob is a well-known businessperson in his town and loves to share his passion for cryptocurrency. Bob doesn’t ever talk about his exact holdings, but it is known that he uses Bitcoin and has a fairly high net worth from his successful car business. Bob worries his home may be targeted for theft. Bob purchases a KeepKey device and sets up his seed phrase. In addition to the seed, Bob generates a strong, random BIP39 “diceware” passphrase (rolling dice to pick words from a list). Bob sends 10 Ethereum and 5 Bitcoin to this main wallet. Bob stores the seed phrase on an engraved steel plate in a hidden location in his home, rather than his document safe in the bedroom. Bob also stores a paper copy of the seed in a bank safety deposit box that is kept secure at all times. The BIP39 passphrase is stored in his encrypted password manager, while his seed is only stored in physical form.
This article was written by our CryptoCurrency Essentials (CCE) Committee, with special thanks to committee member Josh McIntyre.
Other CCE Committee articles:
What is a Cryptocurrency Wallet?
Disclaimer
The information presented in this article is for educational and informational purposes only. It does not constitute financial advice, investment recommendations, or any form of endorsement.
The views and opinions expressed by individuals in this article are solely those of the speakers and do not necessarily represent those of C4 or any other organizations with which they are affiliated.
The mention or inclusion of any individuals, companies, or specific cryptocurrency projects in this video should not be considered as an endorsement or promotion.
Regulations and legal frameworks around cryptocurrencies may vary in different jurisdictions. It is your responsibility to comply with the applicable laws and regulations of your country or region.
